Why Zero-Knowledge Encryption is the best
In this year of our lord, 2022, the term ‘Zero-Knowledge Encryption’ equates to best-in-class data insurance. We’ve already written an article named “What is Zero-Knowledge Proof?”, so we’re not going to look at definitions here, but rather, we’re going to explore the pros and cons of Zero-Knowledge proof encryption when compared to other technologies.
But for those who don’t want to dive deep into technical details, here’s an explanation of what Zero-Knowledge Encryption means:
It simply implies that no one else (not even the service provider) has access to your password-protected data.
This is important because even if your files are completely encrypted, if the server has access to the keys, a centralized hacker attack can result in a data breach.
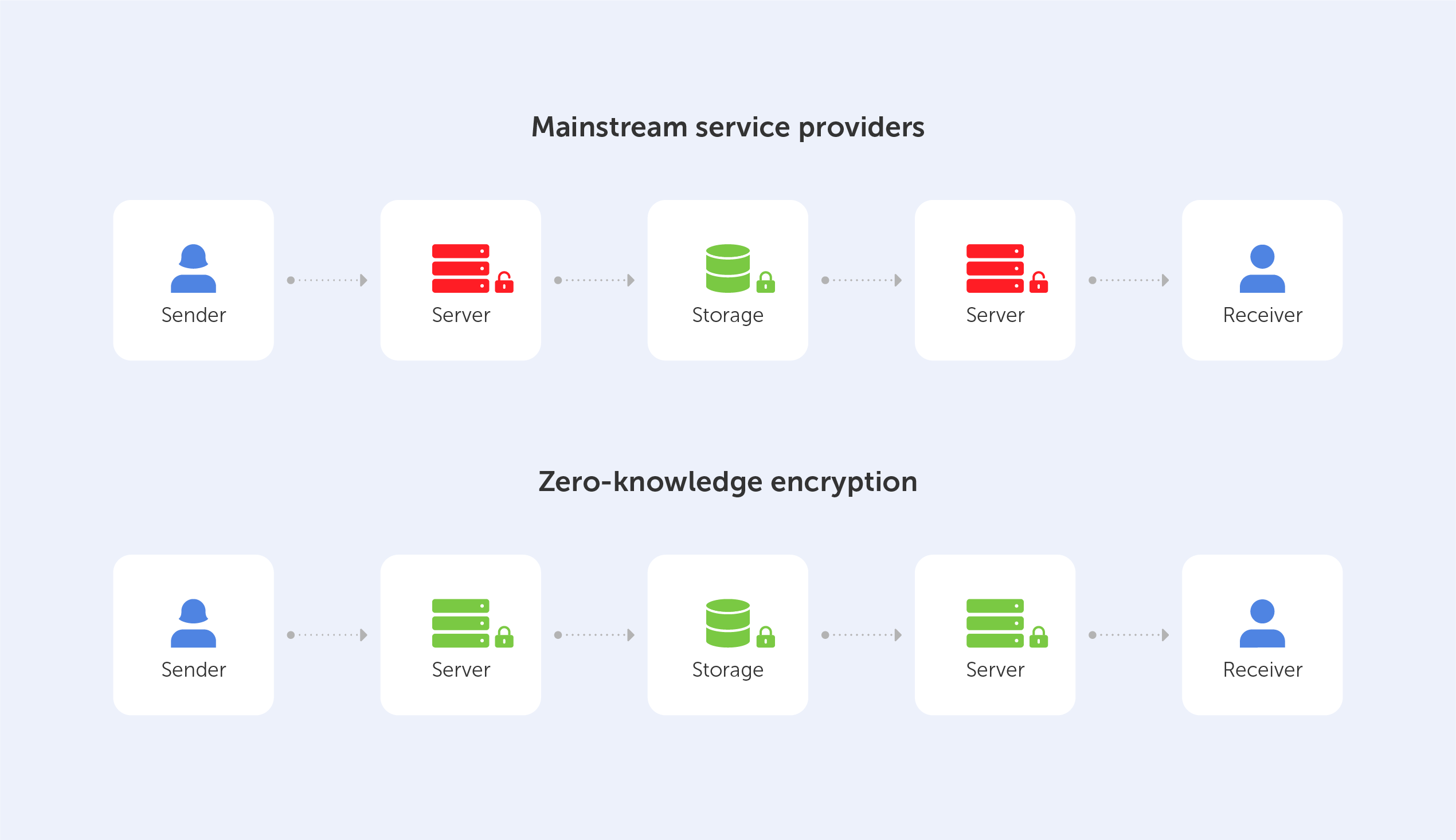
In order to gain a better understanding of the factors that led to the development of Zero-Knowledge Encryption, we've decided to present a succinct, yet comprehensive, assessment of the advantages and disadvantages of three existing options:
Encryption-in-transit
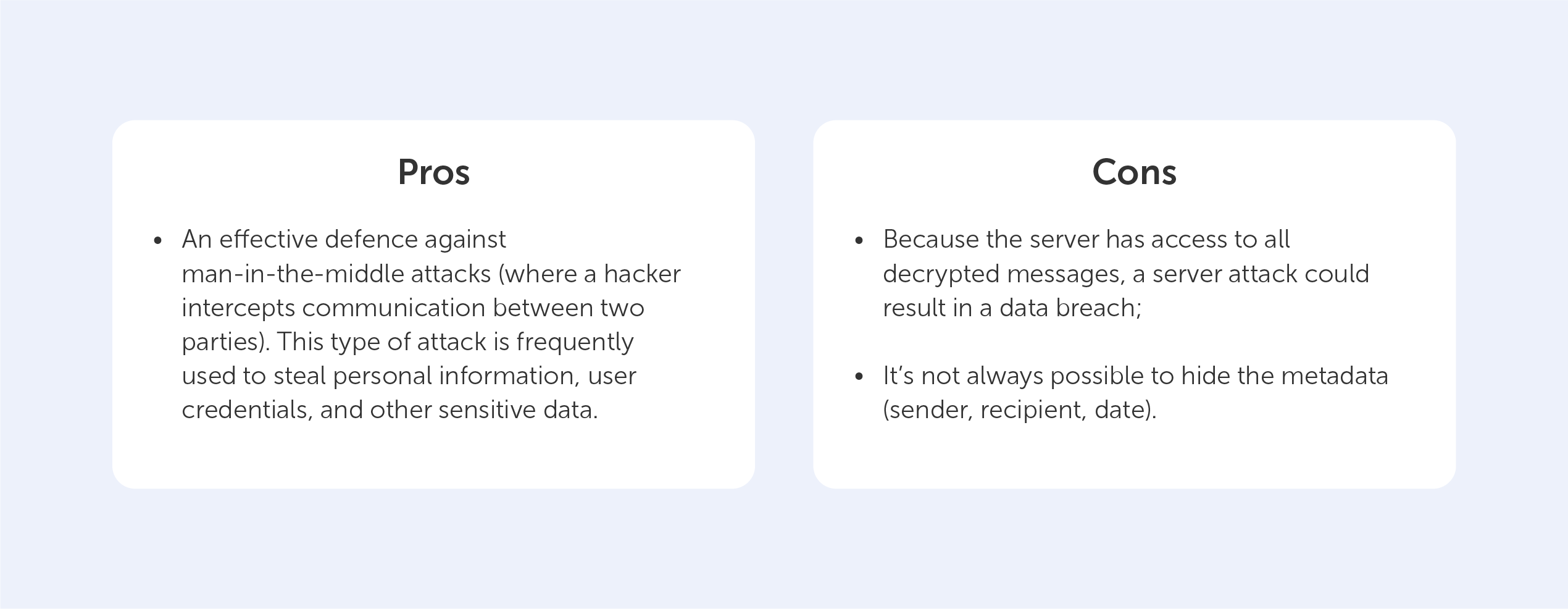
Data in-transit, also known as data in motion, is data that is actively flowing from one point to another, such as that over the internet or over a private network. Data protection in transit refers to the security of data while it is being transferred from one network to another or from a local storage device to a cloud storage device. Effective data protection measures for in-transit data are critical because data is often considered less secure while in transit. Think of it like hiring security guards to accompany your cash-in-transit vehicle’s trip to the bank.
This means that, while using this approach, stored docs are 100% decryptable, so vulnerable.
As for our everyday life, the following technologies use the ‘encryption-in-transit’ approach:
- Transport Layer Security (TLS), which is aimed at ensuring your security on the web;
- Secure/Multipurpose Internet Mail Extensions (S/MIME), which are often used for email message security.
Encryption-at-rest
Any data encryption is the process of converting one type of data into another that cannot be decrypted by unauthorized users. For example, you may have saved a copy of your passport. You obviously don't want this data to be easily accessed. If you store encrypted data on your server, it’s effectively "resting" there (which is why it’s called encryption-at-rest). This is usually accomplished by the use of an algorithm that is incomprehensible to a user who does not have access to the encryption key needed to decode it. Only an authorized person will be able to access the file, ensuring that your data is kept safe.
The Advanced Encryption Standard (AES) is often used to encrypt data at rest.
But, in order to access the data, you need a key — and that’s where the potential vulnerability lies.
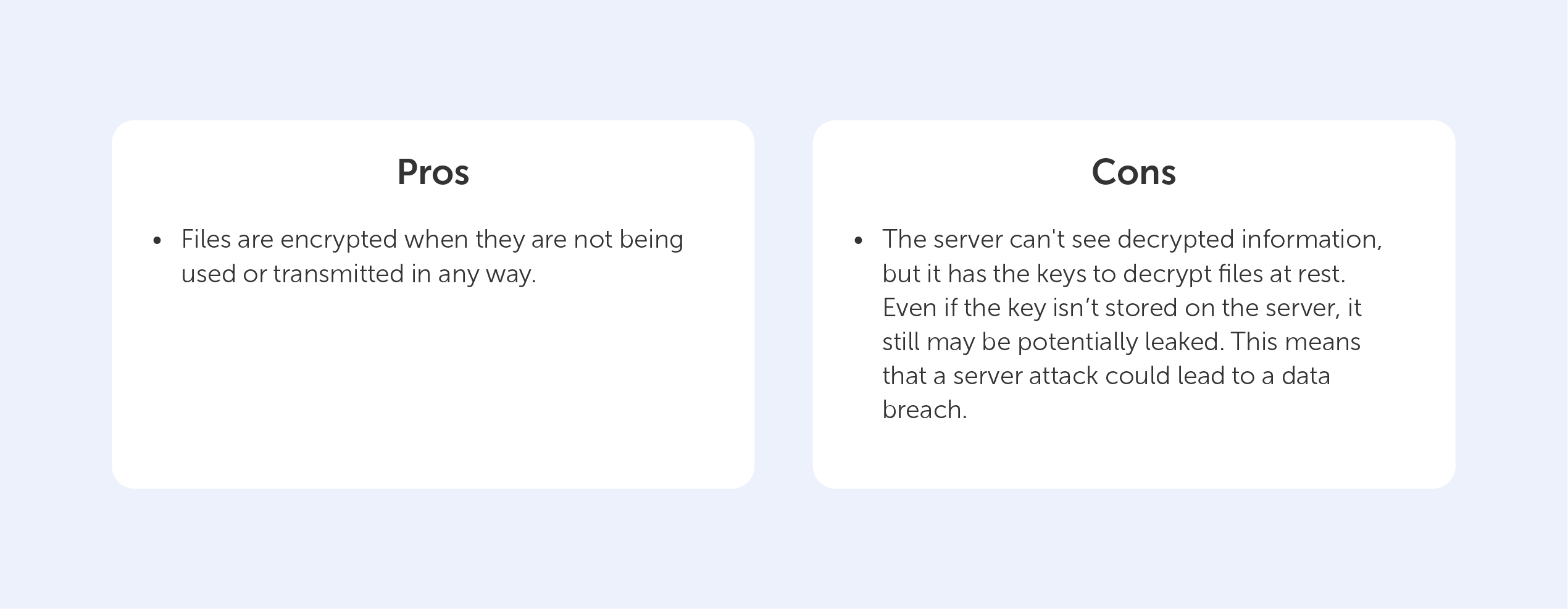
Encryption-at-rest is like storing your data in a secret vault, encryption-in-transit is like putting it in an armored vehicle with security guards for transport.
End-to-end Encryption
End-to-end encryption is the act of applying encryption to messages on one device so that only the device to which it is sent can decrypt it. The message travels all the way from the sender to the recipient in encrypted form.
In practice, it means that only the communicating users (who have the key) can read the messages.
End-to-end encryption has created an impregnable fortress for communication services (for example, messengers), going beyond the security "façade" of encryption-in-transit and encryption-at-rest solutions.
This is the most common approach when protecting oneself against data breaches nowadays, but it only works from "one end to the other," as the term implies. Even though this all sounds great, end-to-end encryption can only be used for a "communication system" like Whatsapp or Telegram.
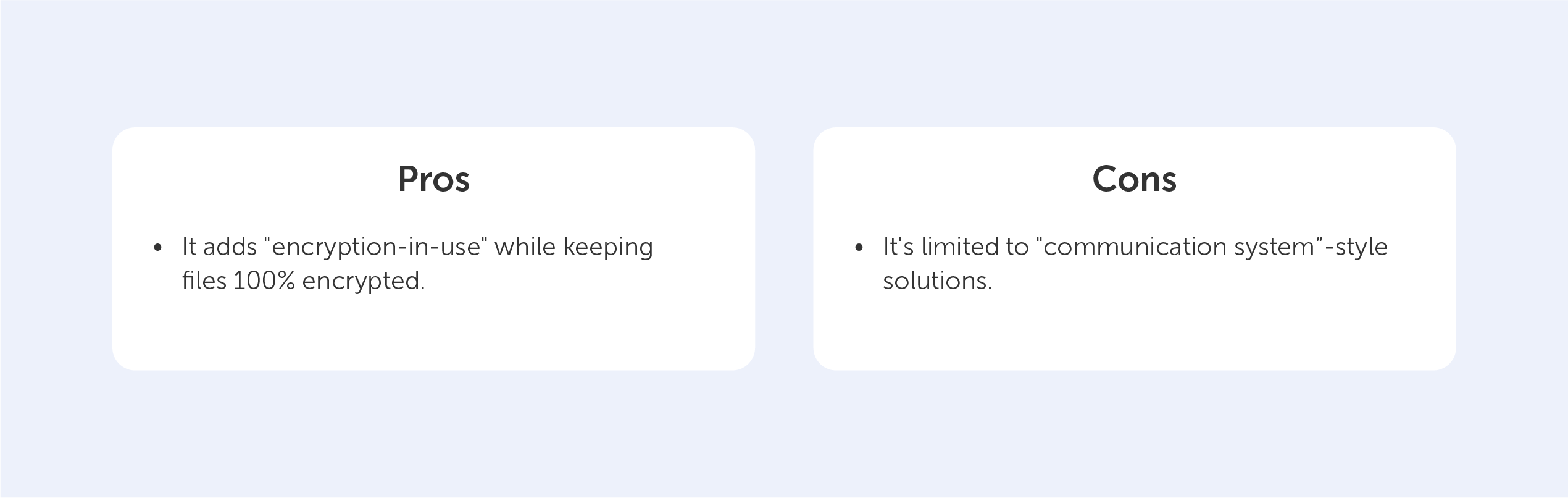
While theoretically sound, end-to-end encryption lacks flexibility, so it can’t be used when the "two ends" that share data don't exist, such as for cloud storage.
This is the motivation behind the development of Zero-Knowledge Encryption, a method that solves the problem by hiding the encryption key, even from the storage provider, resulting in an authentication request without the need for password exchange.
Zero-Knowledge Encryption
To log in to an account, you usually have to type in the exact password. In today's hyperconnected world, it's normal practice to tell the server your secret key ahead of time and test whether it matches.
Instead, there is another, more secure way, to manage this delicate process and that’s called Zero-Knowledge Encryption.
Without diving deep, The Zero-Knowledge relies on three main requirements:
- Completeness — an honest prover will be able to convince the verifier that he has the password by completing some process in the required way;
- Soundness — the verifier will almost certainly discover when the prover is lying;
- Zero-knowledge — if the prover has a password, the verifier receives no more information other than the fact that the statement is true.
Essentially, the system will check to see if you can demonstrate your knowledge several times by responding to various conditions. It’s like a brute force attack carried out backwards — you perform the same action many times in order to make sure that the prover isn’t lying.
Instead of concluding, let’s round up the pros and cons of Zero-Knowledge proof encryption when compared to the alternatives:
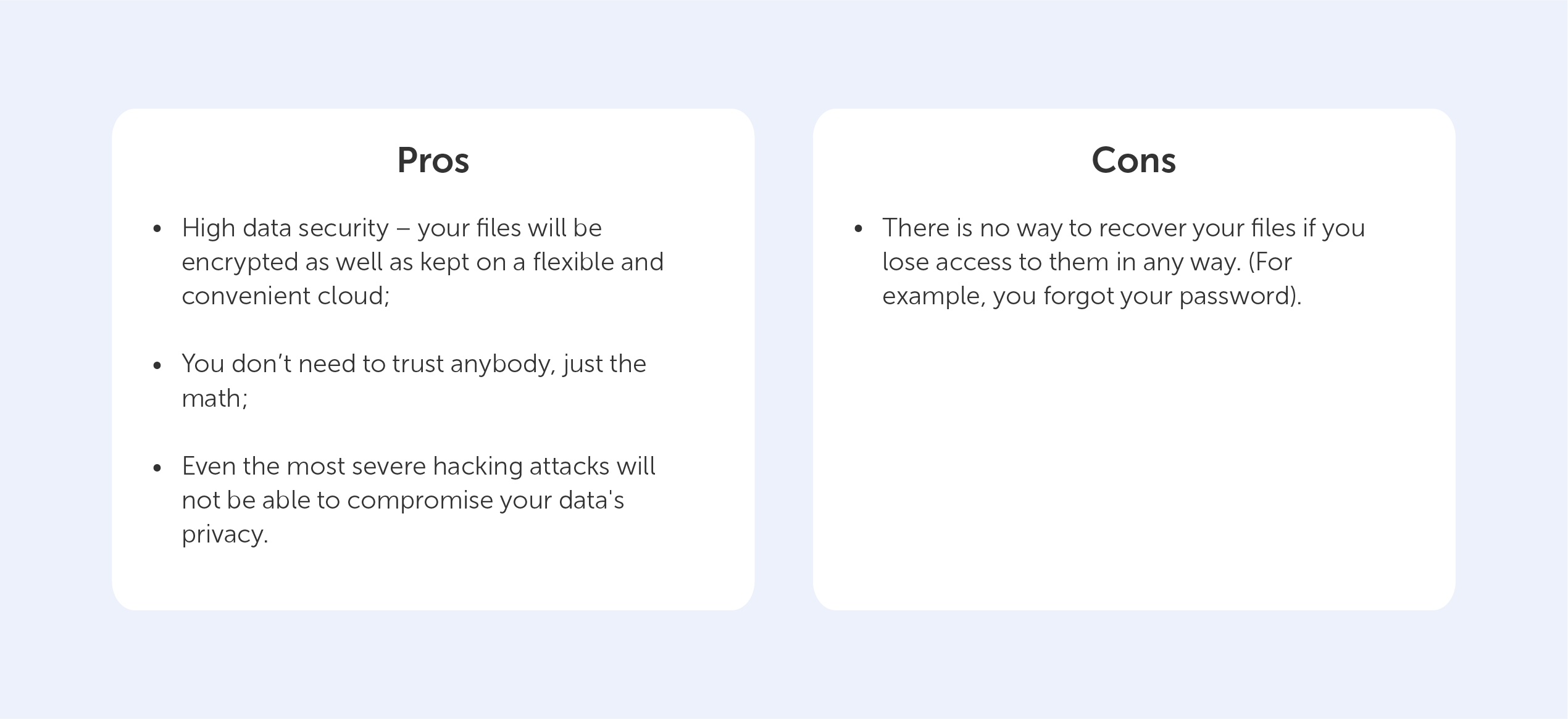
The con here is a clear example of the exceptional security provided by the Zero-Knowledge Encryption solution, which prevents even system administrators from recovering your password. This is why we, at Passwork, rely on this technology in our products. Ultimately, that’s why you can rely on us too.

