What is a VPN?
Why do you actually need a VPN?
Virtual Private Networks (VPNs) encrypt your data and hide your online activity from third parties, allowing you to surf the web anonymously.
Web servers collect information about your computer's IP address and other information about your browsing history when you visit a website that is hosted on their servers. Your data is scrambled and far more difficult for third parties to monitor when you use a VPN that first connects to a private server.
Consumer VPNs are mostly used for anonymous web surfing. Some people can also use a VPN at home to connect to computers and files on your local network from a different place.
What are the possibilities of using a VPN?
Because a VPN alters your Internet Protocol (IP) address, it may perform a wide range of functions. When a computer is linked to the internet, it has a unique IP address that notifies other computers where it is situated. When you use a VPN, you first connect to a remote computer (a server) to fool other computers into thinking you're in a different place. When using a virtual private network, it is possible to choose a fake location for yourself.
PrivacyJournal offers reviews of the best VPN providers out there.
There are many options available to you when you get a new IP address. The material available on streaming services like Spotify and Netflix, for example, can change. Using a VPN allows you to access streaming libraries in other countries.
A VPN may also be used to circumvent censorship. A practice known as geo-blocking may be used by certain government agencies to ban websites and services in certain regions or territories. Through the use of a VPN, you may cultivate the illusion that you’re in a different place, masking your real IP address and as a result, accessing restricted media.
In terms of the ‘dark side’, individuals use VPNs to download copyrighted material and engage in other illicit actions online as there is an obfuscation of responsibility.
Does a VPN provide ultimate privacy?
Encryption is a crucial component of a VPN. All you need to know about encryption is that it scrambles your data so that only the right key can decode it. We'll go into more detail about encryption in the following section. To put it another way, it's a deadbolt lock for your computer's hard drive.
Before it reaches the internet, all of your data travels via an encrypted tunnel, where it is inaccessible to everyone else. As a result, when you visit a website, your browser does not transmit any information along with it. Browsers carry a lot of data, like your time zone, language, operating system, and even your screen resolution.
Although none of this data directly identifies you, the full collection is likely unique to you and may be used to identify you via a technique known as browser fingerprinting. Government authorities, marketers and hackers may use this information against you.
A VPN conceals all of your browser information, as well as your browsing history. While you’re connected, no one, even your internet service provider, can tell what you’re doing online.
A VPN isn’t a one-stop-shop for internet privacy, however. Anything you do while connected to the internet is fair game, including websites you log into and services you utilize. Many browsers utilize an account to move information like your browsing history and cookies between devices. This data isn’t safeguarded by your VPN tunnel, either.
How does it work?
VPNs provide an additional layer of protection for your online activity. As previously stated, using a private VPN server enables you to mask your IP address and make it look as if you're connected to the open internet via a different location.
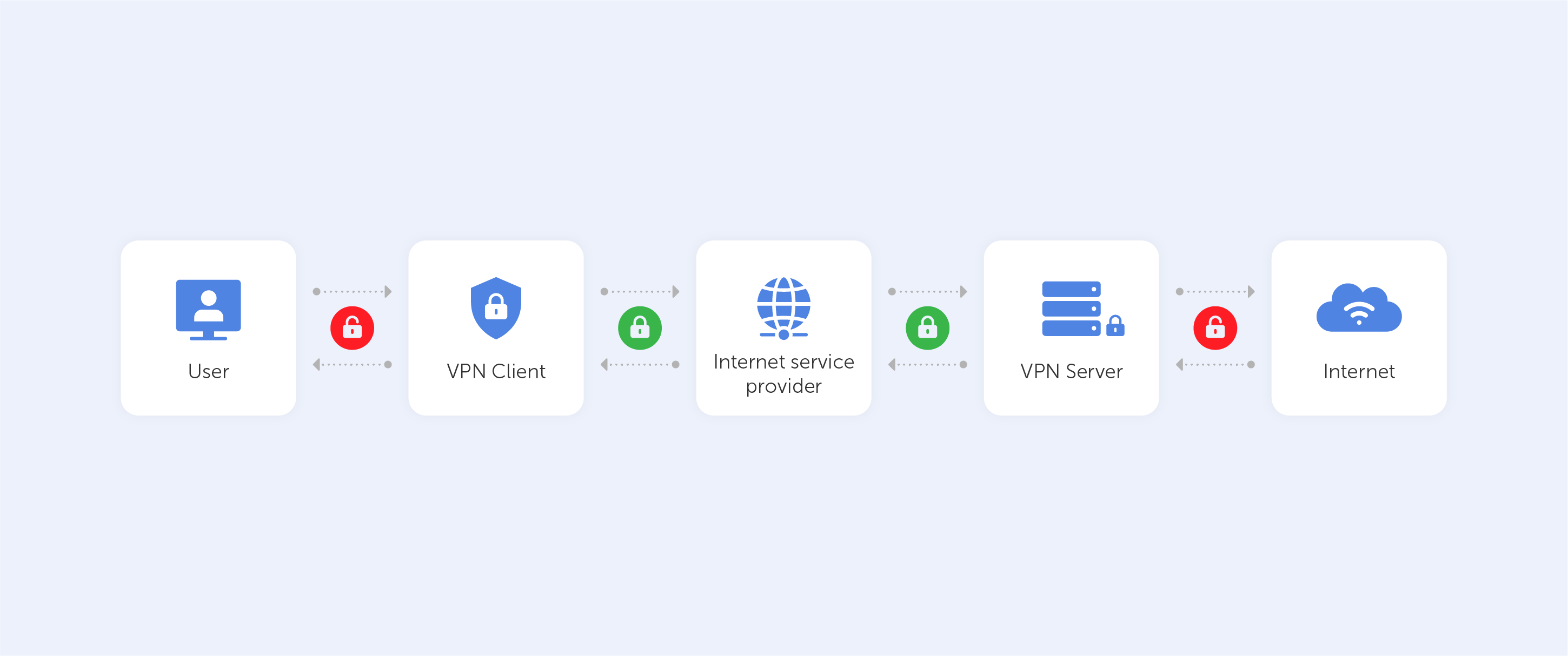
All of this is possible because of VPN protocols, which are used by VPN service providers. VPN protocols are simply a set of instructions for your computer to follow while connecting to a server. The protocol also specifies encryption requirements in addition to a ‘how to’ of setting up and managing your connection.
Encryption is a major reason to use a VPN. All but a small percentage of web surfing now takes place in a secure environment. Despite the fact that you're using an encrypted connection, your personal information is still being sent.
Think of your internet connection as a passageway through which you move information. In order to keep your online activities private, this tunnel is protected by a layer of encryption. Whenever you connect to your Twitter account, for example, you're doing it over a secure tunnel that only you and Twitter can see.
As with a VPN, this is the case. Instead of directly connecting to the internet, your data is routed via a VPN server, where it is encrypted and rendered anonymous. The AES cipher with a 256-bit key is used by most VPN services. AES is a widely used block cipher for encrypting and decrypting data.
By establishing an encrypted connection, the VPN server verifies that you are indeed connected to a certain private network. Data and browser history are then shielded from prying eyes outside the tunnel and never leave it.
To summarize, a VPN creates an encrypted path for your data to travel through on its way to and from the VPN server. In most cases, there’s no way for anybody to know who you are or where you’re from when connected to a VPN server.
Is it a panacea?
When it comes to the effectiveness of VPNs, there's no secret sauce. A renowned VPN service like NordVPN or TorGuard is all you need to ensure that your VPN works. Individual product evaluations are of course necessary.
There's a short test you can do to determine whether your VPN connection is functioning. For free, ipleak.org and ipleak.net provide tools for checking your IP address, DNS queries, and WebRTC data (basically, everything a VPN should, in theory, obfuscate). Verify that the information is different when your VPN is active. As long as it is, your VPN is running as it should.

