Comparison of instant messaging protocols
Since the dawn of the internet, the world of chat programs has seen drastic transformations. Given that not that much time has passed since the creation of the first chat app — CompuServe's CB Simulator — the rate of progress and development is quite astounding.
Chat protocols and frameworks are the subject of this article, and we're going into great detail about everything from their history to their security issues. At Passwork, we’re also very interested in the security solutions that are intertwined with these chat protocols, so without further ado, let’s explore the most popular ones:
WebRTC — Web Real-Time Communication
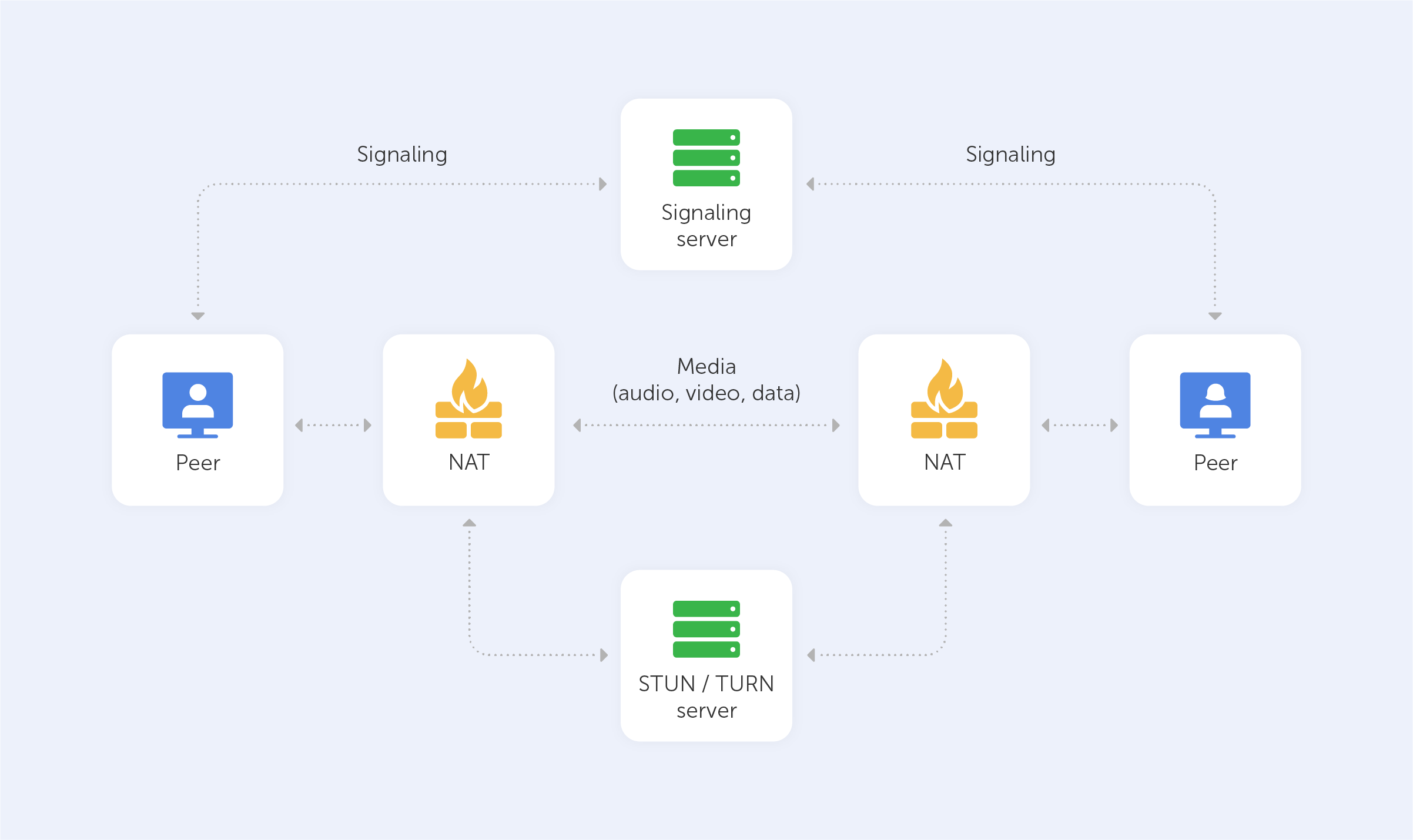
Using WebRTC, you may participate in rich, real-time multimedia conversations. Most web-based video and audio chat systems need you to download third-party plugins or applications. As a result, most browsers already have WebRTC, which utilises APIs to link peers. As an open-source initiative developed by Google, WebRTC enables real-time communication in your web browser.
By default, WebRTC uses UDP (the User Datagram Protocol). However, if there is a firewall between the two devices, WebRTC is able to use TCP (the Transmission Control Protocol).
When it comes to WebRTC, it’s primarily used to provide an immersive multimedia experience without the requirement for third-party applications or services.
Direct and unmediated communication with your consumers is one of the main advantages of WebRTC. If you're looking for complete control over customer communication channels, this is the ideal solution for you. As an additional bonus, there is no rate limit or price adjustments due to the absence of a third-party provider.
To construct a chat solution using WebRTC, you'll need access to a developer who is familiar with the technology.
Discord, Google Hangouts, and Facebook Messenger are just a few of the numerous chat apps that make use of WebRTC.
Security:
WebRTC enforces or supports essential security practises in all major areas since it was, after all, created with security in mind. As a result, in addition to being made safe, it encourages WebRTC developers to take security seriously as well.
WebRTC is now considered by some to be one of the most secure VoIP technologies available as a consequence of a significant emphasis on secure communication. The basic idea of having encryption enabled by default is that a call is always private. Encryption and security are no longer regarded as optional features. To top it off, WebRTC is open source, making it a compelling and dependable platform on which developers may wish to construct their next product.
Of course, we anticipate a rise in the number of communication services that provide significantly enhanced security to their consumers in the near future. But, for the time being, WebRTC is one of the frontrunners.
WebSocket
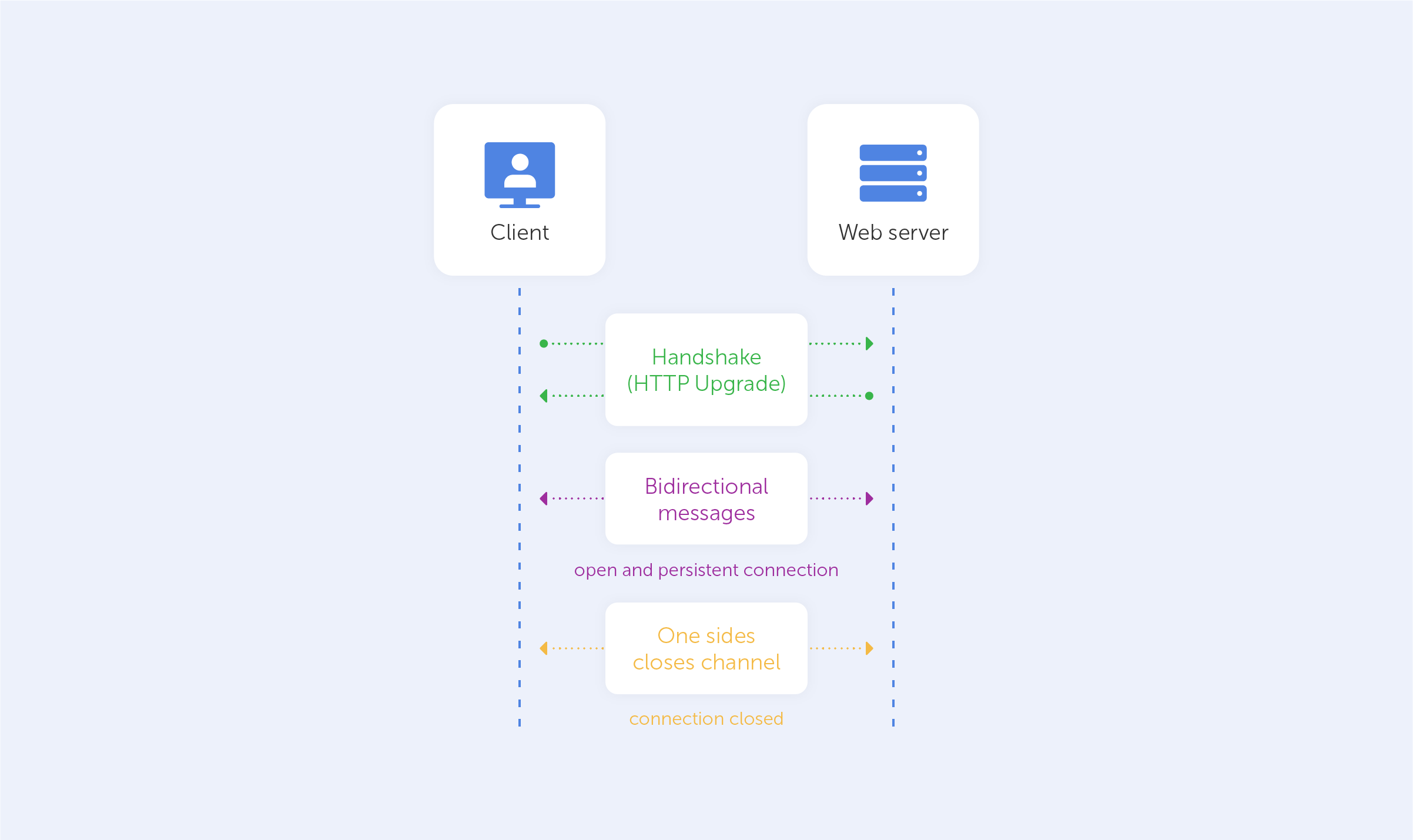
WebSocket, one of the most widely used communication protocols, establishes a low-latency, near-real-time connection between the client and the server via the use of sockets. As it aims to achieve the lowest latency feasible, it is most often utilised for online gaming, chat apps and the real-time updating of social feeds, for example.
In contrast to a standard HTTP system, in which communication may only be started by the client, a WebSocket connection allows communication to take place both ways. The WebSocket API is supported by all current browsers, and data is transferred through a TCP port, similar to the HTTP protocol.
When a series of conversations around the inclusion of a TCP-based socket API in the HTML5 standard began in June 2008, WebSocket was one of the ideas that emerged.
WebSocket is a technology that is used by many websites that demand real-time updates. WebSocket is used by several large chat apps, such as Slack, as part of their technology stack.
Security:
WebSocket as a technology has some inherent security issues:
- WebSocket permits an infinite number of connections with the target server, resulting in the server's resources being depleted as the result of a DOS attack;
- WebSockets may be utilised over unencrypted TCP channels, which can expose sensitive data to serious defects like those described in the OWASP Top 10 A6-Sensitive Data Exposure list;
- WebSockets are subject to malicious input data assaults, resulting in Cross-Site Scripting attacks (XSS).
XMPP: Extensible Messaging and Present Protocol
With the launch of Jabber in 1999, Jeremie Miller brought XMPP to the world.
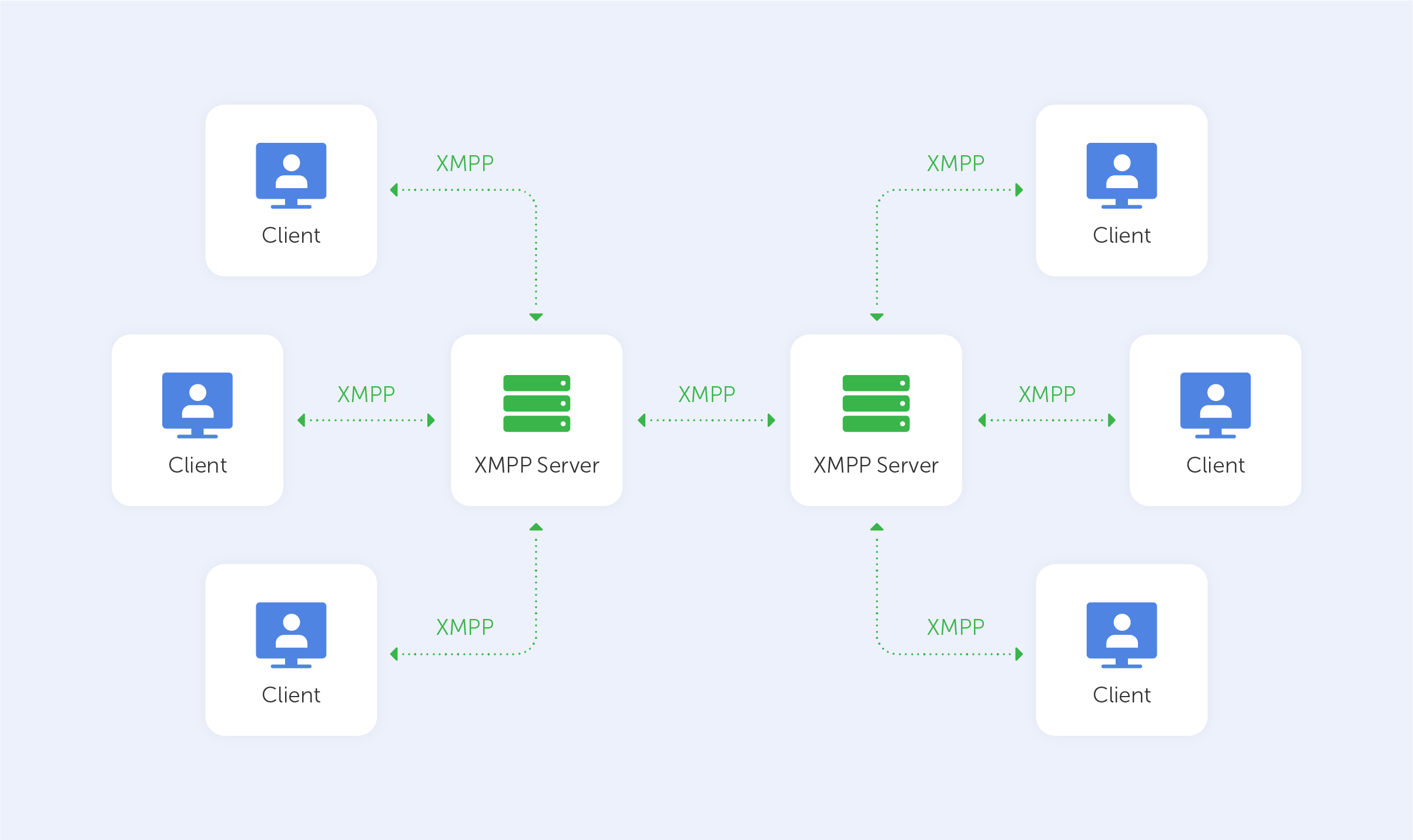
XMPP is a protocol for sending XML (Extensible Markup Language) data over the internet. It facilitates real-time communications by improving the push method between clients. XMPP aims to create a network of linked devices that can communicate with one another using their own trusted servers.
It's a cross-platform protocol that can be used with the XMPP client on the Web, Android, and iOS platforms. The enormous number of open-source and free clients is one of XMPP's distinctive selling advantages, allowing for a very simple installation procedure.
Instant messaging, multi-party conversations, content dissemination, and multimedia streaming, such as audio and video calls, are all examples of the protocol’s applications. Many big chat programs, such as WhatsApp and Zoom, employ XMPP.
Google Talk, ICQ, and Cisco Meeting provide excellent illustrations of what can be accomplished when using an XMPP client.
Security:
XMPP has had its security vetted by the experts at the IETF, and so has native support for pluggable authentication (via SASL) and leading-edge security (via TLS).
Still, that doesn’t stop some hackers from finding vulnerabilities:
An unauthenticated, remote attacker might utilise a vulnerability in the Cisco Meeting Server software's Extensible Messaging and Presence Protocol (XMPP) capability to create a denial of service (DoS) scenario for users of XMPP conferencing apps. The flaw is caused by XMPP packets that haven't been properly validated. An attacker could take advantage of this flaw by sending specially crafted XMPP packets to a vulnerable device, or even by inducing process crashes and denial-of-service scenarios in XMPP conferencing apps — either way, it's not great for the users.
You can read about this exploit more here.

