How to check if you’ve been hacked & the next steps
Almost every user of the internet faces hacking at least once. Cybercriminals have invented a wide range of techniques that aim to crack your password or harvest the credentials and personal data including financial and banking details that are stored on your computer. The timely detection of break-ins may save your privacy and protect your data from being compromised. That’s why you should always be aware of the signs of being hacked and the actions to be taken if you do find yourself in such a situation.
To begin with, it’s important to confirm whether you’ve been hacked or not. Nowadays, the Internet provides multiple ways to do it:
1. Information about almost every cyberattack is available on the Internet. Various news sources publish alerts about data breaches that could be an early indicator that your account has been compromised and that you should take action. Indeed, it’s important to make sure that you have at least one reliable source which provides information about cyberattacks.
2. There is a range of websites available that provide information about every hacked account. One of them is “Have I Been Pwned” which contains a wide database of records about cyberattacks and compromised accounts. To check the security of your account, you should just enter your email address and the system will tell you if your data was the subject of a hacker attack. A positive result doesn’t guarantee that your privacy was violated by cybercriminals, but it does mean that some of your login credentials may have become publicly available.
3. Another powerful tool for ensuring the security of your data is Dehashed.
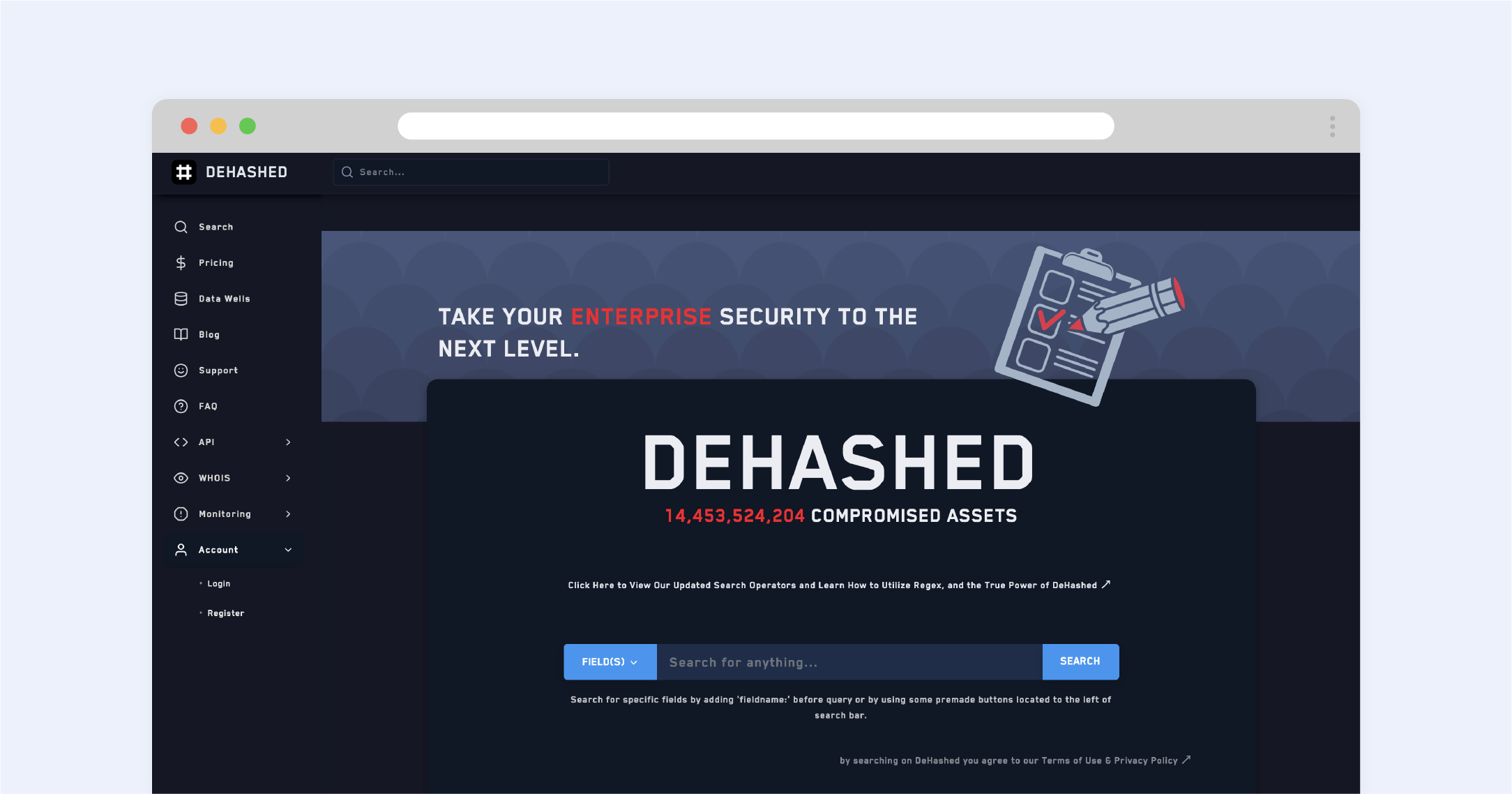
It's a more comprehensive program than the previous one. Just enter any keyword connected to your account like an old username and Dehashed will surf the Internet to check whether that nugget of your private information has been leaked to the public.
4. Most official public apps and sites alert users about access attempts by sending emails or text messages. So, if you get suspicious alerts that someone has accessed your account from a peculiar IP address or at a strange time, check your VPN to make sure it wasn’t you, and if it wasn’t, there’s a high likelihood that you’ve been hacked.
5. To mitigate the risks of being hacked, check the security of sites that you use regularly. There are a lot of tools that can help you to do that. One of the best is the Sucuri Site Checker. To find out if one of your daily used sites was attacked or endangered your private data, you should enter the website link and the program will provide you with information about any threat that the site could pose. If you reveal that the website you use every day is risky, it would be better to change the password of any account connected to that site and also check the safety of your accounts with the tools aforementioned.
It’s also worth checking for suspicious activity on your account manually. Many sites and apps provide the possibility of tracing recent activity and it’s a wonderful way to find out if anyone else has been using your account. This feature gives information about where, when, and from what device you logged in. Frequenting this setting is the thin end of the wedge of successfully protecting your data; it ultimately prevents any undetected interference. If you have some active sessions opened in an unknown place or from an unknown device, you’ll be in the know. Such an issue can simply be solved by changing the password and logging out all existing sessions. Besides, it's better to protect your account by activating two-factor authentication in addition to changing the main password.
What should you do next?
First of all, you should notify your friends, colleagues, and other people you contact through the hacked account to make sure that they don’t fall prey to the activities of your hacker. Most shallow cybercriminals use your account to prolong the hacking chain. They pretend to be you and send messages or emails asking about material help for an ill grandma or for a phone number to send an SMS with a malicious link, pretending that it is needed to recover access to a locked account of theirs. Nowadays, almost everyone knows about such criminal ploys, but elderly people or loved ones often still fall victim. Thus, it’s necessary to alert everybody that someone else is using your account for the purposes of scamming.
The next significant recommendation is not to pay the ransom. If you received a message from the scammer telling you that you have to pay for the safety of your data, just don’t respond and you won’t have to pay. The main reason why hackers breach your account is to get money. If he understands that you won’t pay, they’re more often than not going to leave you alone. But, if you’re still worried about the security of your data, you should contact your local law enforcement agency. Another reason why you mustn’t pay the ransom is that you indirectly promote the hackers' actions; you’re investing in their endeavour and stimulating their activity. Moreover, they might see you as a cash cow and try even harder to extort you in the future.
The next course of action in taking control over your account is changing your password. Indeed, use your noggin to figure out which sites may use the same password, and change those passwords too; it goes without saying that you shouldn’t reuse the same password on multiple websites. It’s also worth using a password generator to acquire new passwords, consisting of sophisticated alpha-numerical combinations that are naturally hard to guess.
In some instances, cybercriminals will anticipate these steps if they feel that their cover is blown, and they’ll beat you to changing your password. In this situation, you should contact the site’s support team to prove that you’re the true owner of the account. Sites such as Facebook will ask you to upload a proof of ID, for example. To prevent hacking from happening in the future, it’s worth taking advantage of the ability to link your email address and phone number to your account.
Recovering access to the account is time-consuming, as all the information ought to be checked manually. So, if you get in such trouble and find yourself waiting to get back your account, take some time to reflect on getting yourself a good-quality password manager that will eliminate the burden in the future. Hint hint.

