Why your passwords are no longer secure (Part 1)

Nearly 20 years ago, the National Institute of Standards and Technology (NIST) established guidelines for secure passwords. Indeed, they are still used by many websites, portals, and other services. You’re likely familiar with these password requirements — there ought to be at least 8 characters, both capital and lowercase letters, digits, and special characters. Despite these guidelines, passwords that meet these requirements are no longer safe from modern attackers. The only thing any of us can do to improve the security of our accounts is to make sure that our passwords are lengthy, complicated, and unique for each account. Due to the strict password management requirements, this strategy is, nevertheless, laborious and intimidating for many.
The Same Password Rules Do Not Apply Today
In the modern day, password-based security is no longer seen as sufficient. Our digital world is continuously expanding, thus it is more important than ever to make sure that our data is safeguarded from cybercriminals. Cybercriminals perceive an opportunity to target people in a more sophisticated way as a result of the increasing usage of internet services. One explanation is that, although we benefit from technological improvement for our personal, social, or economic growth, cybercriminals have also benefited from the advantages of improved computer graphics cards and machine learning to enhance their attack strategies. In addition to the problem of more sophisticated cyberattacks, there are two interrelated problems with conventional password rules:
The first concern lies in our human nature — keeping track of passwords is tough
You may take a few steps as an individual to increase the security of your passwords. Start by lengthening and making your passwords more complicated. Second, create a unique password for each website you visit. The difficulty of remembering a password increases with its complexity. As a result, we frequently select passwords that are not entirely suitable yet are simple to remember. The difficulty of managing several complicated passwords for every online account leads to the frequent reuse of the same passwords across multiple platforms. As a result, a successful attacker immediately wins big.
However, the high level of password complexity necessary to maintain online safety should not be blamed; rather, it should be pointed out that we can’t improve our inadequate password management skills. Using a password manager to generate and store secure passwords is a useful solution. It is not humanly possible to manage strong passwords for all of our internet accounts without assistance, such as password managers. Because they can't recall the complicated, random sequences of letters, numbers, and special characters, the problem increases the likelihood that individuals will write down their passwords. Passwords are left exposed in digital files stored on a computer or in desk-top notes, making it simple for hackers to hack and read passwords.
The second problem is that passwords have a mathematical limit
There are only ever a finite amount of potential password combinations since a password is a mix of letters, numbers, and symbols. As a result, the best technique for breaking passwords is brute force attacks. Until the correct combination is identified and the password is broken, brute force attacks attempt all possible combinations of letters, numbers, and symbols. Theoretically, a stronger password would be one that is harder to guess due to its length, complexity, and number of possible permutations. However, attackers are now substantially more frequently exploiting Graphic Processing Units (GPUs) to break passwords. GPUs are a component of a computer's graphics card and were first designed to speed up the loading of images and movies. They now show promise for computing hashes (the method used in brute force attacks).
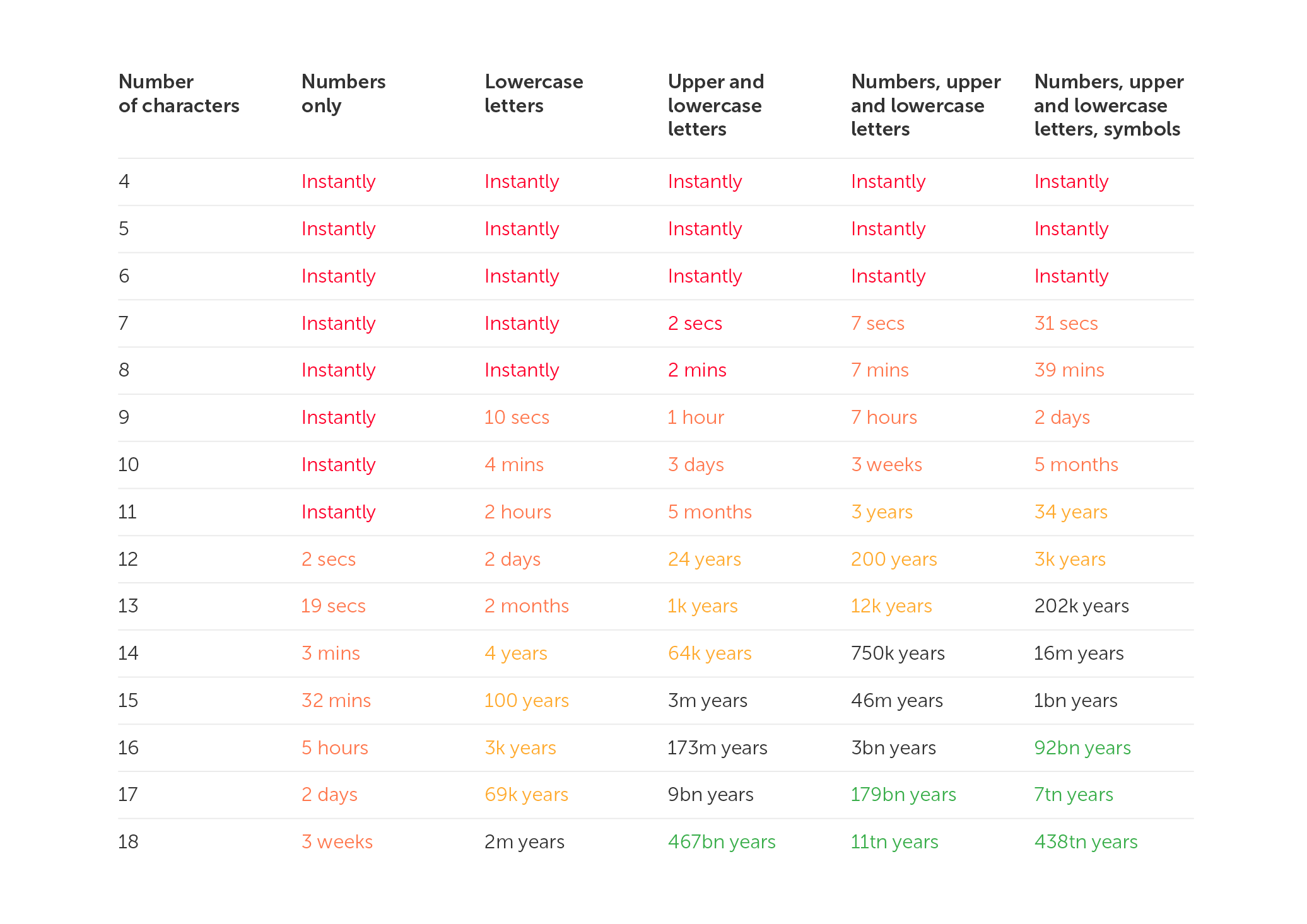
According to studies on password cracking times, passwords may be cracked much more quickly using sophisticated computer graphics cards. Using the most recent computer graphic cards, an 8-character password that used to take 8 hours to crack in 2018 now only takes 39 minutes (see the conclusive 2022 results in the table below). Passwords are gradually getting simpler to crack as a result of recent technical developments, which is a concerning trend. More crucial, however, is the fact that if a password has already been stolen, repeated across sites, or contains basic phrases, attackers may access your accounts right away, regardless of the complexity of the password or the attacker's graphics card.
Consider a 4-character password made up of all 26 letters in the Latin alphabet (case-insensitive) in order to visualise this mathematical example.
26^4 = 456,976 possible password combinations
The number of viable choices rises to when you include digits, uppercase and lowercase letters, and special characters.
95^4 = 81,450,625 possible password combinations
However, because the password must contain at least one special character, one number, one capital letter, and one lowercase letter, the quantity drops to
5,353,920 possible password combinations.
Nevertheless, assuming there are no password-entry security measures, this can be cracked in less than a second by a computer (such as automatic account blocking).
Increase the length and complexity of passwords
Longer or more complicated password phrases are strongly advised when creating new passwords. In this manner, potential attackers will have a harder time breaking the codes. It's crucial to take into account the popularity of the selected password combination in addition to the amount of alternative password combinations. For instance, lists of frequently used passwords or phrases, such as "qwerty," "password," or "12345," are frequently used in brute force assaults.
Therefore, the password should be completely unique or not contain any words at all. For instance, one technique would be to employ acronyms or mnemonics, such as generating a password out of the first few characters of a long text. As an illustration, consider making the password ‘Ilts@7S!’ out of the words I love to ski at Seven Springs.
Password length and complexity alone are insufficient
We are aware that adding length and complexity to passwords is the only method to increase their strength and, consequently, the safety of our accounts. The time it typically takes an attacker to break a password in 2022 using a powerful commercial computer is displayed below. This chart, which has been analysed and periodically updated since 2018, shows how quickly passwords can be broken on current machines. This pattern indicates that, despite our best efforts to create passwords that are longer and more complicated, passwords alone are no longer sufficient to meet the required internet security standards.
In conclusion, password rules increase the complexity of passwords without necessarily enhancing their security. The answer to that is to use no passwords at all. However, we’ll discuss that in part 2 of this article.

