The history of encryption. Confrontation of encryption and intelligence agencies.
Since the time of the Roman Empire, people have been able to use encryption to keep their communications private. When the Roman emperor Gaius Julius Caesar was penning an important message, he would sometimes replace a letter in the source text with another letter that was positioned three characters to the left or right of the original letter in the alphabet. This practice dates back to well before our period. If the communication was intercepted by his adversaries, they would not be able to decipher it since they would think it was written in some other language. This method of concealment was known as the Caesar cipher, and it was categorized alongside the other substitution ciphers. The substitution ciphers' overarching strategy is to change the meaning of a character by using a different character.
However, in encrypted messages, common terms were replaced by a single letter, eliminating the possibility of substitution. In this manner, Mary Stuart, imprisoned in Sheffield Castle, communicated with Anthony Babington about the conspiracy and Elizabeth's death. This is a part of that letter.
Indeed, Elizabeth's counterintelligence department, commanded by Francis Walsingham, intercepted the letter, which was quickly decrypted by Elizabeth's greatest cryptanalyst, Thomas Fellipes. How did he manage it? Through an analysis of frequencies.
All letters appear in the language with varying frequency. As a result, you just need to define the percentage of characters in the text that will be replaced by a certain character, and it will take some time to substitute and test hypotheses. This is called frequency analysis. It only works on somewhat long texts, and the longer the text, the better.
Anthony Babington was hung, drawn and quartered, Mary Stuart was beheaded, and the process of letter replacement was no longer deemed secure. However, an antidote to frequency analysis was discovered immediately. It is sufficient to utilize several encryption methods: encrypt one string with one, and the other with another, and frequency analysis will be rendered ineffective.
Since then, there has been an ongoing race between encryption and cipher cracking.
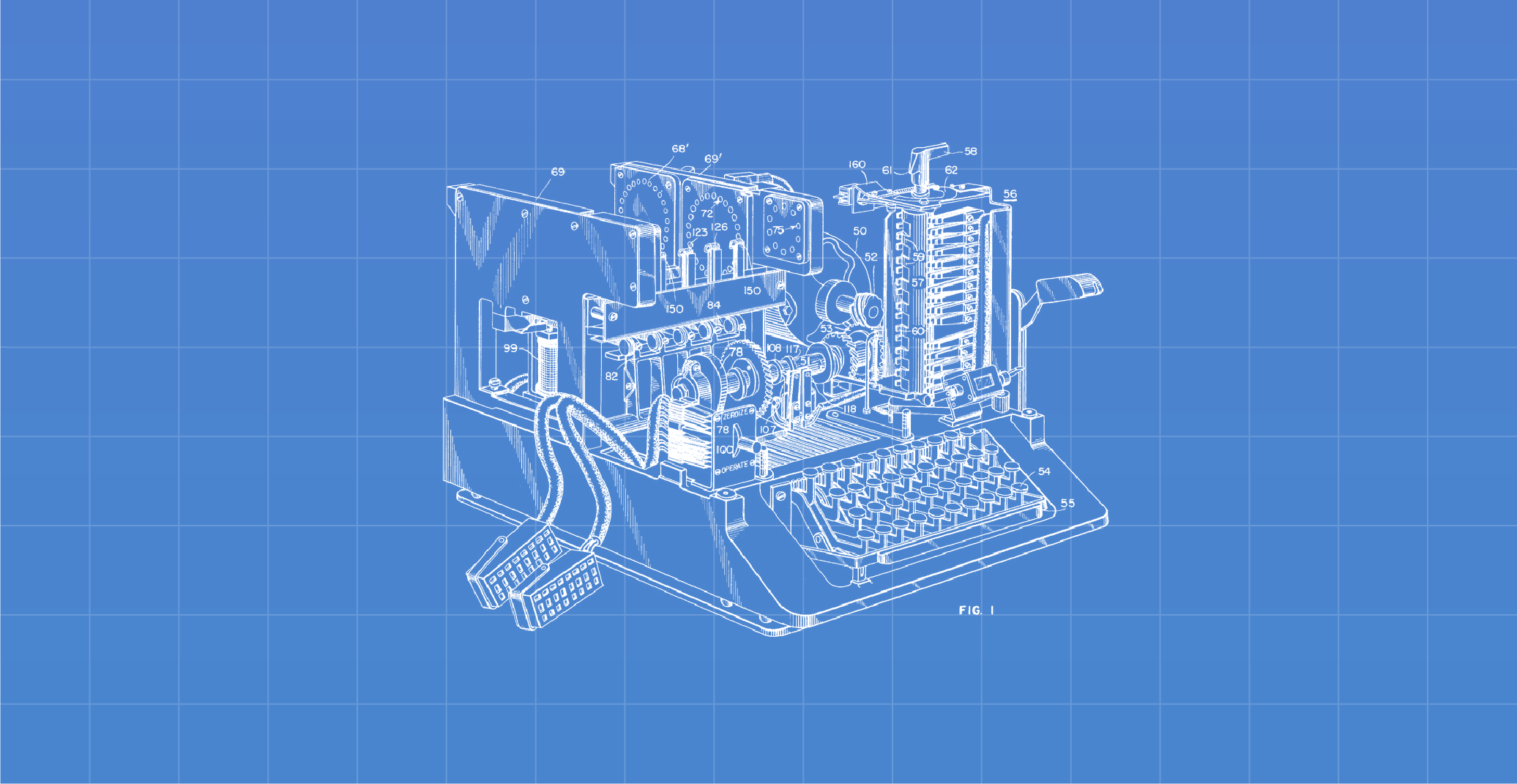
The cracking of the Enigma cipher machine used by Nazi Germany to safeguard military and political communications is the most notable feat in breaking encryption algorithms. By the standards of the time, it was a superb encryption device, on which the brightest brains in Germany collaborated. But deciphering the encryption required no less of a force: a team of British cryptographers collaborated with the young scientist Alan Turing.
Despite the cloak of secrecy, his name is linked to the selection of the key that could unlock the Enigma. Indeed, the key was a seemingly mundane Hitler greeting, which had to be included at the conclusion of every piece of correspondence. Alan Turing accomplished the impossible by providing his country with a crucial advantage during World War II.
Modern algorithms like AES, Twofish, and Blowfish differ significantly from substitution or the displacement of letters, as well as Enigma ciphers. Furthermore, they have nothing to do with them and are immune to brute-force and frequency analysis attacks. One thing stays constant, however: there are still individuals who wish to hack them and decipher encrypted messages. Nowadays, the availability of such a dependable data protection instrument cannot help but bother those who wish to acquire access to any information of special services.
Methods of attacks on ciphers by intelligence agencies
Today, intelligence agencies use three primary methods to attack ciphers.
Direct key selection to ciphers
Data centers that use brute force to break encrypted data are being created for this purpose. You can crack practically any contemporary encryption by brute force; simply guess the key (which is generally logical: if there is any key, in theory, sooner or later it can be guessed). The only question is how much power you have and how much time you have. For example, whereas a single contemporary computer can check 10,000 keys per second on average, a data center of thousands of machines may match tens of millions of keys per second.
Fortunately, cracking a powerful cipher can take more than a dozen years in a contemporary data center, and it is impossible to envision what has to be done so that a whole data center is engaged in cracking your encrypted data. After all, a single day in a data center costs tens of thousands of dollars. Because of the expense of resources, a basic password selection using a dictionary is generally done.
This was the situation with Daniel Dantas, a Brazilian banker who was detained in Rio de Janeiro in July 2008 on accusations of financial fraud. Five hard discs with encrypted data were discovered during a search of his flat. Local specialists were unable to break them and went to the FBI for assistance. The FBI returned the CDs after a year of futile attempts. The method of picking a password using a dictionary was utilized for hacking. Daniel Dantas devised a strong password that would be immune to dictionary assaults. It is unclear whether this aided him in court, but access to his encrypted data was never acquired. He utilized TrueCrypt, an encryption application, by the way.
Aside from data centers, there is an ongoing development of a quantum computer that has the potential to drastically revolutionize modern cryptography. If cryptographers' forecasts come true, it will be easy to crack any current crypto container very fast following the advent of such a supercomputer. Some scientists believe that such a supercomputer has already been developed and is located someplace in the hidden cellars of the US National Security Agency.
The second attack method is a scientific study of modern encryption algorithms with the aim of breaking them
A lot of money is being invested in this business, and such decisions are truly invaluable for special services and intelligence. Here, researchers compete with intelligence agencies. If researchers break the protocol or discover a weakness early on, the rest of the world is likely to learn about it and switch to more secure methods. If they are discovered by intelligence agencies, they are discreetly utilized to obtain access to encrypted data.
A 768-bit RSA key was regarded as an entirely reliable solution ten years ago, and it was utilized by private users, huge corporations, and governments. However, a consortium of engineers from Japan, Switzerland, the Netherlands, and the United States successfully computed data encrypted using a 768-bit RSA cryptographic key at the end of 2009. The usage of 1024-bit RSA keys was suggested. However, 1024-bit RSA keys are no longer deemed strong enough either.
The third attack method is a collaboration with device, program, and encryption algorithm creators to weaken encryption and add backdoors
It is sufficiently difficult for special services to decrypt a correctly encrypted crypto container, so instead, they try to bargain with firms producing encryption tools so that the latter leaves decryption flaws or degrades the algorithms utilized. The US’ NSA is ahead of the rest of the world in this regard. According to Edward Snowden's allegations, the American creator of cryptographic technology RSA Security was paid $ 10 million by the NSA to build a backdoor into its software. RSA Security provided its clients with the notoriously flawed Dual EC DRBG pseudo-random number generation technique for this money. Because of this flaw, US spy services were able to readily decode communications and information.
We don't know what additional backdoors exist in encryption algorithms today, but we do know that decrypting information is one of intelligence services' top goals. High-level professionals are continually working on it, and governments are pouring money into it. It is well known that the majority of efforts are focused on cracking SSL protocols, 4G security technologies, and VPNs.

